Microservices Architecture: Security Strategies and Best Practices
Over the past few years enterprises and industry leaders have been steadily adopting microservices to drive their business forward. At this point, companies like Amazon, and Google, to name a few, must agree that the microservices style of architecture is much more than a passing trend.
Along with the many benefits of updating monolith systems to microservices architecture, there are also new security challenges that organizations need to address. It’s important to remember that microservices require DevOps, development, and security teams to adopt new security patterns and practices to ensure microservices security.
What Are Microservices?
Microservices — or microservice architecture, are an architectural style that divides the traditional monolithic model into independent, distributed services that can be scaled and deployed separately.
Martin Fowler and James Lewis describe microservices as “an approach to developing a single application as a suite of small services, each running in its own process and communicating with lightweight mechanisms, often an HTTP resource API.” They explain that microservices “are built around business capabilities and independently deployable by fully automated deployment machinery. There is a bare minimum of centralized management of these services, which may be written in different programming languages and use different data storage technologies.”
Source: https://microservices.io/patterns/microservices.html, by Chris Richardson.
Securing Microservices Architecture
Fowler and James provide a list of common characteristics of microservices, including smart endpoints and dumb pipes, decentralized governance and data management, and infrastructure automation. This new type of highly distributed and dynamic system presents teams with a new set of potential security risks that need to be addressed, and require them to adopt a new security approach. As with many arising technologies, security needs to be baked into architecture patterns and design and integrated into the entire development lifecycle, so that applications and data remain protected.
Think Strategy: How To Secure Microservices
As microservices architecture continues to evolve at a rapid pace, along with the application security ecosystem, it’s important that organizations adopt a few interconnected key approaches that will help them keep their microservices security patterns up to date while remaining agile.
#1 Defense in Depth
One strategy that’s important to adopt is defense in depth. Gone are the days depending on a single firewall to protect your monolith system. Defense in depth is a security strategy that calls for placing multiple levels of security controls throughout an organization’s software systems. In the context of microservices, the services with the most sensitive data are the ones that require multiple, and varied, layers of protection.
#2 DevSecOps
Second but just as critical is the DevSecOps approach. Like all components in the DevOps pipeline, microservices security requires DevSecOps tools and practices. These include shifting security left by integrating application security testing tools into the entire DevSecOps pipeline, from design all the way up to production.
#3 Isolation
Gavin Kenny of IBM stresses the importance of isolation as a core principle of microservices: “Each service must be an autonomous piece of the overall application puzzle. A microservice needs to be able to be deployed, maintained, modified, scaled and retired without affecting any of the other microservices around it.” He adds that this extends to the support functions beneath the architecture, like the database level, and that isolation is also important in failure mode.
Patterns and Best Practices for Microservices Security
There are a number of best practices for integrating microservices security patterns, helping teams update their APIs, endpoints and application data. Here are 7 best practices for ensuring microservices security.
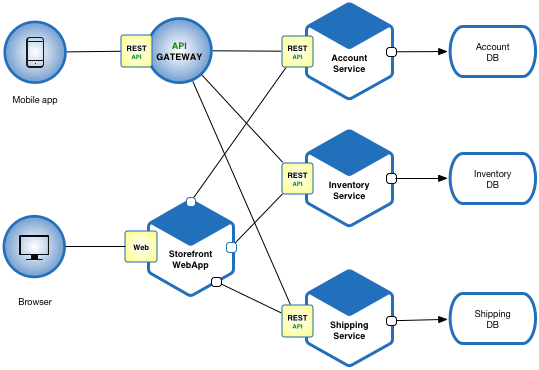
#1 API Gateways
One of the most vulnerable areas of microservices architecture patterns are the APIs. When putting together microservices security best practices, building API gateways is critical, even more, when you’re dealing with more than one. These act as a single point of entry that handles external requests, helping to block a client’s direct access to microservices, and preventing potential attacks from malicious actors.
#2 User Authentication and Access Control
Since securing endpoints is extremely important when it comes to microservices security, user authentication and access control are critical parts of a solid microservices security plan. Experts recommend OAuth/OAuth2, a popular standard, for user authorization. Multifactor authentication is also important in securing your application, both for prevention and detection, since it helps block malicious players, and also provides warning when an intrusion occurs.
#3 Scan Dependencies
Third party and open source components make up most of the software that we create today. These include a tangled web of dependencies that are impossible to track manually. This becomes an issue when a dependency contains a security vulnerability. It’s important to track third party components and open source components, including all of their dependencies, in order to detect and remediate security vulnerabilities as soon as possible.
#4 Application Security Testing Tools
Speaking of vulnerable dependencies, as the number of security vulnerabilities continues to rise every year, it’s important to integrate a variety of black box and white box application security testing tools throughout your DevSecOps pipeline. These might include SAST (static application security testing), DAST (dynamic application security testing), RASP (runtime application self-protection), and SCA (software composition analysis tools) throughout your DevSecOps pipelines.
#5 Container Security
In the cloud-native environments where microservices reside, container security is key. This applies to the entire containerized environment, including container images, registries, and orchestration. Happily, DevSecOps offers us a number of automated container security technologies and tools to easily integrate into your environments.
Staying Ahead of Microservices Security
Cloud native environments are evolving quickly and introducing many new trends to the software development industry — and microservices are one of them. Microservices bring easy scalability and agility to today’s fast paced digital world. It’s important to remember not to let security fall by the wayside as we speed and scale up our systems.
The security strategies and best practices listed in this post should give you some ideas of how to tighten up your microservices security plans. It’s important to remember that like many of today’s evolving technologies, it’s important to find the right fit for your organizations, depending on your architecture and existing systems. Just as important to your microservices security game is to work as a team to constantly track and monitor the security processes and tools that you implement, and update them when necessary.
